Modern facility management involves establishing a secure perimeter that goes significantly beyond traditional locks and keys. In a professional corporate environment, the movement of staff, contractors, and visitors must be managed with absolute precision to maintain safety and operational efficiency. Advanced digital frameworks are now the standard for securing sensitive assets in offices, data centres, and industrial sites across Singapore. These systems verify identity through various credentials to ensure that only authorised personnel gain entry to specific areas.
A professional entry framework combines physical barriers with digital intelligence to create a thoroughly controlled environment. Evaluating these options requires facility managers to consider how various hardware components and software platforms work together to prevent unauthorised access. From the initial authorisation methods to the backup systems that ensure a facility remains protected during unforeseen events, every component plays a role in long-term stability. By following a structured design and installation process, organisations can achieve operational continuity and peace of mind.
Key Takeaways:
- Define clear security zones to manage internal and external traffic effectively.
- Invest in durable hardware that supports modern encryption and safety standards.
- Prioritise power redundancy to maintain security during local electrical outages.
- Utilise structured cabling to ensure fast and reliable data transmission.
- Integrate entry controls with surveillance for enhanced situational awareness.
Categorising Entry Management Hardware
Selecting appropriate authentication methods is the first stage of the procurement process for any commercial facility. Modern security door access control systems can range from standalone card readers for single entries to enterprise-level networked solutions managing hundreds of points across multiple locations. Common methods include proximity cards, smart fobs, and mobile credentials stored on smartphones, which allow administrators to manage entry permissions remotely. Each hardware choice must be evaluated based on the specific traffic volume and the security risks associated with different zones.
Biometric readers provide an additional layer of verification by scanning unique characteristics such as fingerprints or facial features. These sophisticated setups ensure that the person presenting the credential is the actual authorised individual, which is essential for high-security environments like financial institutions or data centres. Modern IP-based solutions often allow each door to function as an independent node on the network, which improves overall reliability by preventing a single failure from disabling the entire system. Choosing the right hardware balance is key to creating a system that is both secure and convenient for daily users.
Infrastructure And Structured Cabling Standards
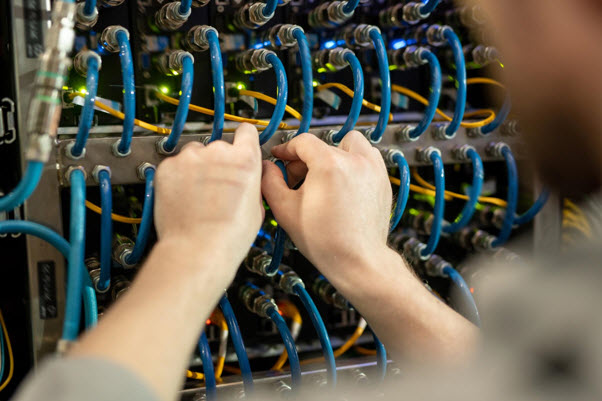
The reliability of an electronic security setup is fundamentally tied to the quality of its physical connections and underlying wiring. Using structured cabling provides an organised and standardised framework for carrying data and power between readers, controllers, and the central server. Unlike disjointed or ad-hoc wiring, a structured approach uses high-quality copper or fibre optic links that follow strict industry standards to reduce the risk of signal interference. This methodical installation simplifies future maintenance and allows for easier system expansion as the organisation grows.
Professionals frequently seek network cabling Singapore services to ensure their infrastructure can handle the demands of real-time security data. Certified network cabling services ensure low-latency transmission, which is essential for modern authentication methods that require instant verification against a remote database. Keeping power and data cabling separated is a critical best practice to avoid electromagnetic interference that could lead to network instability. A stable cabling foundation provides a seamless experience for employees and a more responsive environment for the facility management team.
Redundancy And Power Management Best Practices
A significant vulnerability for digital security networks is their total reliance on the local electrical grid. If a building loses power, electronic locks will either default to an open state, compromising security, or stay locked, which could trap personnel inside during an emergency. To mitigate this risk, designers incorporate uninterruptible power supplies into the central control panels to keep hardware functional until main power returns or a generator takes over. This redundancy ensures that high-security areas are never left vulnerable during a blackout or electrical malfunction.
A well-specified UPS power supply filters out electrical noise and protects sensitive controllers from power surges that might otherwise damage internal circuitry. Proper power management involves regularly testing these backup units as part of a preventative maintenance schedule. This small step makes a huge difference in system uptime, ensuring that the uninterruptible power supply is always ready to engage during an emergency. By prioritising power continuity, organisations can support critical access functions and preserve their digital infrastructure during local electrical faults.
Site Surveys And Pre-Installation Planning
Conducting a proper site survey is the first stage of any professional access control system installation. The guiding principle for specialists is that nothing is done by force before drilling, wiring, or mounting any equipment. This initial review focuses on evaluating the client's specific security requirements and assessing the property layout. By identifying potential cable routes and evaluating existing electrical infrastructure, installers can plan a setup that avoids unnecessary modifications and ensures long-term performance.
Specialists must also determine the exact number of entry points and the types of doors or gates that require monitoring. In complex environments like a GPON hotel, this preparation phase is particularly important to ensure seamless connectivity across multiple access points. Teams that arrive fully prepared with the correct tools, hardware, and cabling materials can complete the installation more efficiently with minimal disruption to daily operations. A well-executed site survey ensures the final system is tailored to the building's architecture and operational needs.
System Integration And Visual Verification
Connecting door readers to a closed-circuit television network allows for visual verification of every entry attempt. When a credential is used or a door is forced, the system can automatically direct nearby cameras to record the event and alert security personnel instantly. This integration creates a complete audit trail that is invaluable for incident investigation and insurance purposes. Effectively communicating between these systems requires a unified software platform that allows administrators to view logs and live feeds from a single dashboard.
Modern access solutions also integrate with fire alarm panels to ensure automatic releases during an emergency evacuation. Final checks include verifying that all doors lock and unlock as expected and that software logs accurately mirror real-world entry activity. Final inspections ensure all components are securely mounted and aligned with safety standards to deliver a dependable smart entry system. By combining various tools into a single ecosystem, facility managers can achieve a higher level of situational awareness for their assets.
FAQs
- What is the difference between fail-safe and fail-secure locks? Fail-safe locks automatically unlock when power is lost to prioritise life safety, while fail-secure locks remain locked during a power failure to prioritise the security of assets.
- Why is an uninterruptible power supply necessary for door entry? Without a backup source, an electronic system becomes inactive during a blackout, which could leave the building open to intruders or trap occupants inside during an emergency.
- How does structured cabling improve a security network? It provides a standardised wiring system that reduces signal interference and ensures data from readers reaches the server quickly and reliably for real-time authentication.
- Can I manage my building security from a mobile device? Yes, most modern networked systems offer mobile apps or web-based dashboards that allow administrators to view logs, grant visitor access, or initiate lockdowns remotely.
- What are the benefits of mobile credentials over physical cards? Mobile credentials are more difficult to lose or share, and use the security features of the smartphone, such as biometrics, to verify identity.
Read another Article: Ultimate Access Control System Installation Guide